
Even the most avid security enthusiasts sometimes get confused when it comes to differentiating between vulnerability management and vulnerability assessment. So, here is a detailed blog underling the fine differences between the two.
Table of Content
What is Vulnerability Management?
In this evolving world of complex IT landscape, we get to hear numerous cyber security buzzwords and strategies every day. Vulnerability assessment, penetration testing, vulnerability management are among the most used terms when we talk about the protection of critical assets in an organization. But ever wondered do these terms mean? Let’s break them down one by one.
The term vulnerability management is an essential component that is required in creating an organization’s solid cyber security foundation. It is a broad ongoing process that manages an organization’s vulnerabilities constantly in a holistic manner. In this cyclical process, the software vulnerabilities are discovered, assessed, remediated and verified. Follow the image to understand the vulnerability management process cycle more clearly.
This ongoing process requires scanning to assess the vulnerabilities continuously in order to ensure and fix the weakness. It is an integral part of computer and network security.
What is Vulnerability Assessment?
The foremost step to fix security vulnerabilities is to identify them in the first place. Vulnerability assessment security testing identifies the gaps and loopholes present in the networks, endpoints, and applications. It is a one-time security testing program that is performed with a defined start and end date.
Vulnerability assessment is a risk-based approach where it targets the different layers of technology such as the host layer, network layer, and the application layer. The purpose of this testing is to help organizations in identifying vulnerabilities existing in their software and IT infrastructure before any compromise takes place.
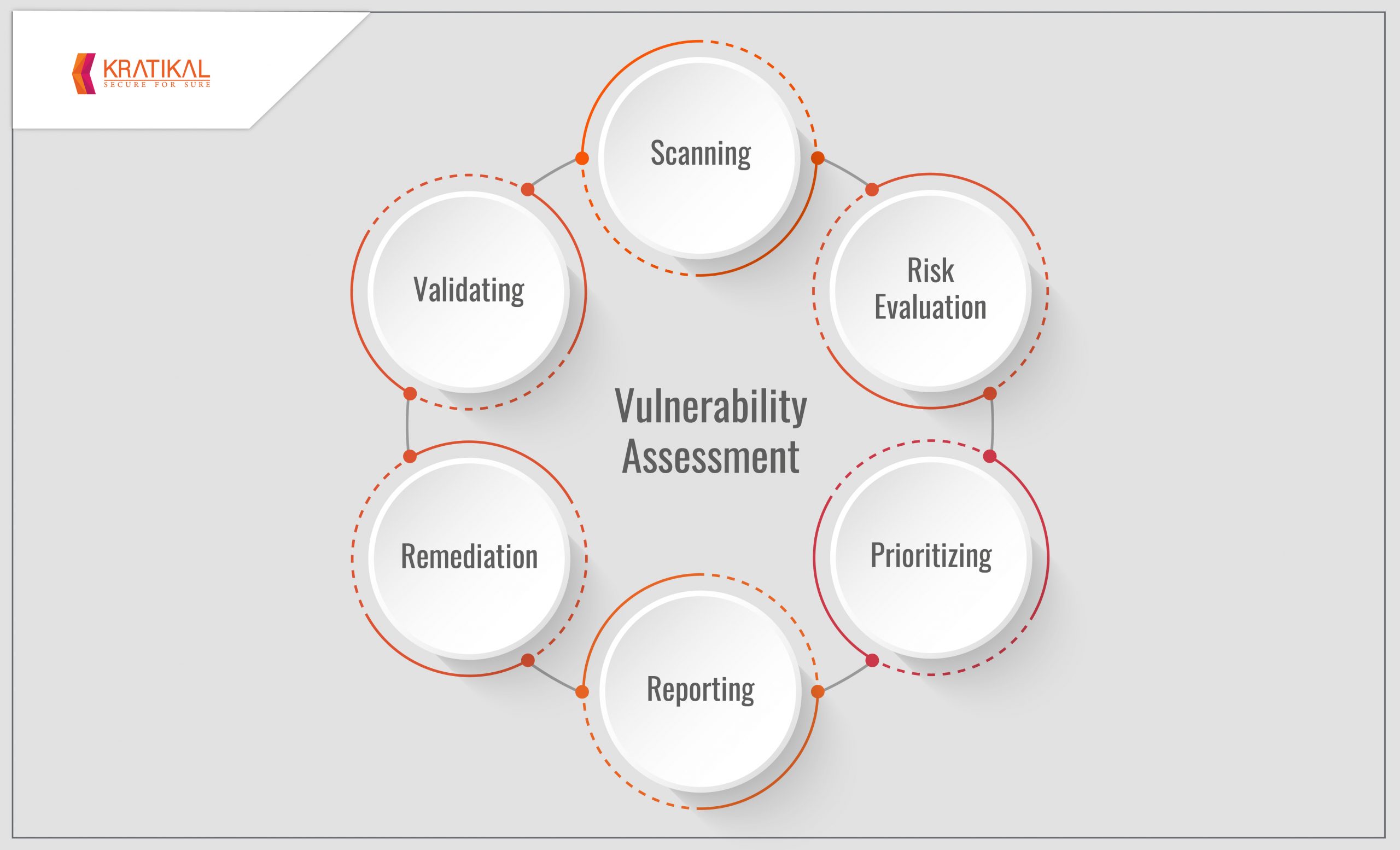
The following image above shows the in-depth evaluation of security posture in an organization, discovering weaknesses and recommending a suitable remedy to mitigate the risk.
Vulnerability Management vs Vulnerability Assessment
When we talk about the entire organizational cyber security, both vulnerability management and vulnerability assessment have their own significant roles. However, both processes are completely different in nature.
Unlike vulnerability assessment, the vulnerability management program doesn’t have any defined start and end date. It is more of a continuous process that helps organizations in having better management of vulnerabilities in the near future.
Whereas, vulnerability assessment, on the other hand, helps in identifying the loopholes and vulnerabilities which are ranging from critical designing to basic misconfiguration. The primary objective of this testing is to create guidance for assisting developers with fixing the identified vulnerabilities.
Although the vulnerability assessment is an important step in improving the IT security of an organization, it is not just enough. A proper ongoing process is required along with this assessment technique to successfully eliminate the security gap.
Interdependence of Vulnerability Assessment and Management

Consequently, the vulnerability assessment process has a start and end date. But in order to secure IT assets, an ongoing approach like vulnerability management should be a part of it. The identification of strengths and weaknesses identified through assessment testing is basically the beginning process of IT infrastructure security. It is more of a part of vulnerability management where a proper plan is required to be created for prioritizing and mitigating the cyber risks discovered. On the whole, the vulnerability assessment dictates the recommendations and objectives of the entire vulnerability management process.
The Significance of Security Risk Assessment and Management
It is important to assess and fully-manage cyber risks with the vulnerability assessment and security testing audits to secure the organization’s network security. With constantly evolving cyber attacks, it is highly important to understand the weakness existing in your IT infrastructure or web applications.
Regularly performed vulnerability assessment and proper vulnerability management practices play the role of cornerstones in the success of a complete cyber security program. Timely discovery of cyber threats help in patching networks as well as web application vulnerabilities. Also, both assessment and management security programs mitigate the risk elements and help in preventing the possibilities of following cyber risks:
- Data breaches
- Ransomware infections
- IT Infrastructure damage
- Reputation damage
- Financial loss
Did we miss out on any important distinguishing features between vulnerability management and vulnerability assessment? Let us know in the comments below!


Great Article !