As the world is battling COVID-19 in the third year of the pandemic, the work-from-home culture has become a parallel mechanism to run organizations. To administer work from home, the organizations have gone under vigorous technological transformation and digitization. Thus, it has become important for organizations to ensure cybersecurity during work from home.
However, working from home culture has its own drawbacks. Offices are secured with strong cybersecurity infrastructure, along with a dedicated security team that monitors suspicious activities. Despite stringent monitoring, cyber attacks still occur in organizations. One can imagine how vulnerable cybersecurity becomes when employees work from home.
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Why is Cybersecurity Important During Work From Home?
The security of all computing devices in remote work or working from home is quite marginal compared to what it is in the office. The primary reason behind this is that computer systems are not well-protected at home. Home networks are pretty vulnerable, and that’s why they require additional security measures such as WLAN encryption.

The concept of online work has evolved over time. This has increased the dependency of employees on devices and networks for communication. Also, these devices and networks are not generally secured enough to prevent cyber attacks. Along with that, employees are easily manipulated or lured when they don’t have ready support from the IT department.
Statistics on Cyber Threats During Work From Home?
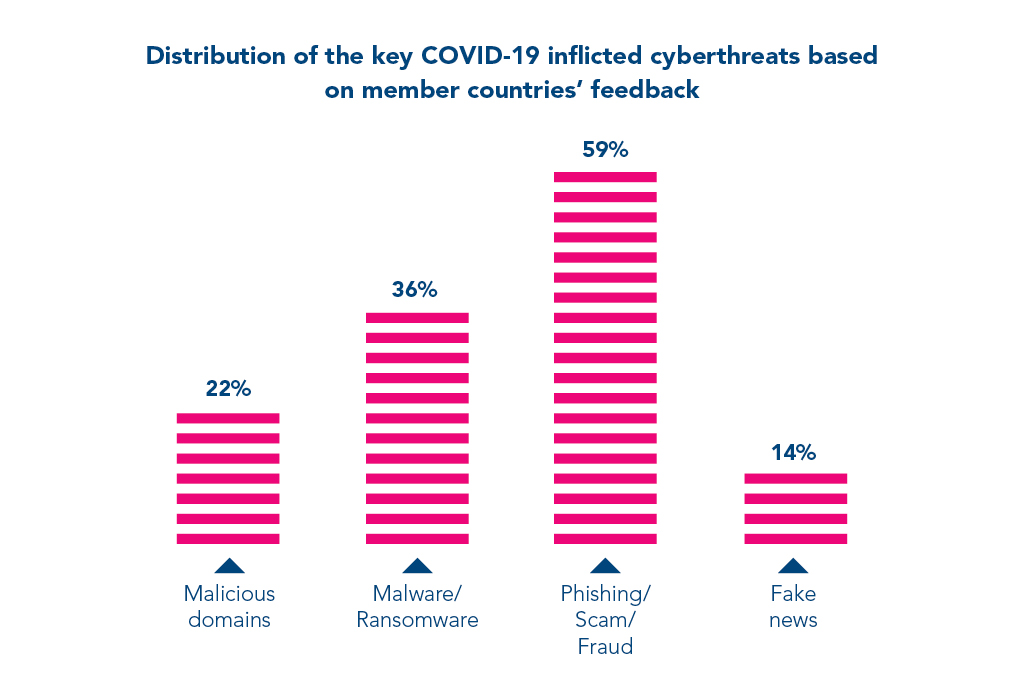
According to IT Governance, 70% of employees during work from home have experienced some kind of cyber threat. Between February and March 2021, the number of phishing emails increased by 600%.
According to IBM, 20% of organizations have reported that work from home was the factor in data breaches. This incurred a loss of $4.96 million on average for the companies. In the same article, it was mentioned that the shift to work from home has increased the average cost of the breach from $3.89 million to $4.96 million.
Best Practices to Mitigate Risks During Work From Home
Following is the list of practices that an organization must follow to prevent cyberthreat and mitigate cyber risks.
1. Provide Cybersecurity Awareness to Employees
Employees must be provided with the knowledge to identify cyber attacks, such as phishing emails, and risks associated with the use of public Wi-Fi. This should be done to ensure the security of the devices being used for work.
2. Secure Medium of Communication
Always use a secure medium of communication for official purposes. Make sure that security protocols such as DMARC are set on your email domain to secure it against any attempt of spoofing or abuse.
3. Deploy a Phishing Incident Response Team
The majority of cyber attacks occur via emails. Therefore, a “Phishing Incident Response” tool is the need of the hour. A single vigilant employee can save the entire organization. A phishing incident tool empowers employees with the capability to report suspicious emails.
4. Deploy a Virtual Private Network (VPN)
Deploy a VPN for secure data transfer between the core system and work systems that employees are using remotely. It adds an additional layer of security by encrypting data while traveling.
5. Virtual Desktop Infrastructure (VDI)
VDI allows employees to work in a virtual environment as if they were connected to the company’s local network from any place, at any time, and from any device that is connected to the Internet. With VDI, data is stored on a server rather than on an individual system. Not only does it significantly lower risks to data, but also, a lesser amount of bandwidth is required to store it.
6. Encourage Employees to Use Cloud Services
Encourage employees to use cloud services like Google Docs, Google Sheets, etc., since this minimizes the risk of data loss since it is not stored locally.
7. Implement a Mobile Device Management (MDM) solution
Deploying an MDM solution helps the organization retain control over business-related sensitive data. The solution allows administrators to remotely lock the devices and wipe all the data in case the device gets stolen. This prevents sensitive data from falling into the wrong hands.
Cybersecurity Awareness Training is Essential for Employees
Currently, hackers and cyber attackers are taking advantage of the coronavirus pandemic by resorting to emotional manipulations. For example, employees receive messages where attackers impersonate renowned medical insurance companies, offering victims a COVID-19 insurance plan for a minimal investment.
Employees click on a lucrative but fraudulent URL received through the phishing email. This link redirects them to a phished login page that asks them for their corporate credentials.
Employees in an organization are usually unaware of cyber attacks and their related consequences. They are unaware of the latest trends and techniques used by cybercriminals and easily fall prey to such threats.
That’s why it is important for all employees to have cybersecurity awareness training so that they can become vigilant and capable of preventing cyber attacks. Employees can specifically take attack vector-based training to repel most cyberthreats.
