Technology has made everyone’s life very easy. People can get anything with just a click and can also keep data in one place. However, it has also become a nightmare as well, as it made it easy for hackers to steal data through phishing attacks. Nowadays this problem is getting worse because of the immense increase in cybercrime.
Hackers use different types of social engineering attacks, phishing is one of the most infamous social engineering attacks. It is widely adopted by hackers for luring victims to reveal their sensitive and confidential information. Phishing attacks are generally carried out through the medium of emails
Subscribe to Our Newsletter On Linkedin
Sign up to Stay Tuned with the Latest Cyber Security News and Updates
Attackers forge fake emails with malicious links. Once the link is clicked and the victim submits its credential, the attacker gains unauthorized access by misusing those credentials. Hence, the victim gets phished.
History of the Emergence of Phishing Attacks
The history of phishing is quite old. It has been prevalent since the good old days of the 90s. America Online (AOL) was one of the top internet service providers during the mid-90s with millions of visitors every single day.
Attackers or ‘Phreaks’ (yes! That’s what attackers used to call themselves. Fancy, right?) started trading pirated software over AOL and formed a ‘warez’ community.
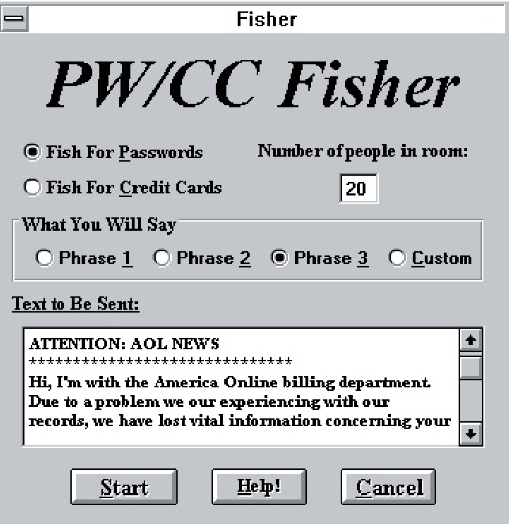
This community stole AOL users’ passwords, created random credit card numbers, and spammed users.
This process was automated with the help of windows software AOHell. Once discovered, AOHell was shut down by America Online.
There are many cases that have been reported and even more that have not been reported. On average, 1.2 million phishing attacks occur annually. According to security research, phishing attacks almost doubled to 482.5 million from 246.2 million in the year 2017. Statistics show that phishing accounts for 91% of all cyber attacks.
Phishing Attacks Lean on Psychology
A typical phishing email isn’t as “rudimentary” as it may seem if you look closer, as you’ll soon discover.
Even the most careless phishing emails usually try to influence the recipients’ perceptions. Although with pretty horrible punctuation and grammar. If their emails meet certain criteria, criminals know they have a good chance of enticing victims to open them. Criminals often use well-known methods of leverage in their phishing emails to persuade recipients to take unusual behaviors, including loyalty, regularity, social proof, and trust. So, hackers incorporate need or discounted offers into such phishing emails like Black Friday or hiring for a position.
It is also possible for phishing emails to succeed by exploiting the human tendency to obey rules which is why CEO fraud is so common. There is a disturbingly simple way to commit CEO fraud: criminals pose as authority figures and demand that their accounting teams transfer immense sums of cash.
It proves that psychological factors frequently play a role in why phishing scams are successful. It has been said that 95% of the scams have happened because of human errors, they have been called the biggest risk in cybersecurity. So, organizations should adopt phishing training for their employees to keep their data secure.
Why do Attackers Use Phishing Attacks?
Large User base
One of the biggest reasons for the success of Phishing attacks is the widespread use of emails. At present, there are around 2.6 billion email users and this number is expected to cross 4.2 billion by the year 2022. The susceptibility rate of phishing attacks is quite high as attackers can easily find out email addresses, and send phishing emails, and there, it’s done.
Humans are the weak link
The other big contributor to the success of phishing attacks is the victim itself. These days, social media has become a huge part of people’s lives. People are putting out their entire lives online. Attackers can easily access the personal information of the victim through a social networking platform that helps in creating personalized phishing attacks (also known as Spear Phishing).
Lack of awareness
Lack of security awareness among employees is also one of the major reasons for the success of phishing. Organizations should be aware of how the benefits and purpose of security awareness training can secure their employees from falling victim to phishing attacks.
In recent years, attackers have shifted their focus from individuals to employees within the organization. Statistically, 90% of cyber attacks are the result of employee negligence. During the year 2018, a 76% increase in the number of phishing attacks was observed.
54% of the companies had experienced one or more attacks that compromised their IT infrastructure and data. According to the survey done on 19,000 people, approximately 97% of the people are unable to identify such attempts.
To mark Cybersecurity Awareness Month, Threatcop collaborated with 31 respected CISOs and CTOs from prominent organizations. Together, we’re working towards a safer digital future.
Explore Here: 31 Cybersecurity Awareness Ideas from Security Leaders
Leniency in the adaption of security measures
The leniency in the adaptation of security measures is one of the biggest reasons for the success of phishing attacks. Studies have shown that organizations lag in spending money on the implementation of cybersecurity measures. During the year 2018, 51% of the organizations have made no change to the budget allocated to ensure cybersecurity.
These reasons play a huge role in the success of such attacks. Therefore, it is extremely important for organizations to implement cybersecurity practices and understand the benefits of following security measures properly. Cybersecurity companies like Threatcop, ensure that your network and infrastructure are secure from cyber attacks. Threatcop offers industry-leading tools such as Threatcop security awareness training (TSAT), Threatcop phishing incident response (TPIR), and DMARC authentication (TDMARC).
