With the intensity and frequency of cyber attacks on medical devices rising every day, the growing significance of cyber security in the healthcare industry is clearer than ever. When it comes to the security of healthcare organizations, there’s much more at risk than just money or data.
Many of the successful cyber attacks on healthcare institutions can be attributed to the vulnerabilities in medical devices such as pacemakers and insulin pumps. Malicious actors can exploit these vulnerabilities to disrupt the clinical performance of medical devices, potentially causing severe harm. In 2007, Dick Cheney’s pacemaker had its wireless features disabled to prevent potential assassination attempts.
The VAPT team of Kratikal, a CERT-In-empanelled security auditor, has conducted security assessments for a wide range of medical devices.
Table of Contents
Vulnerabilities in Medical Devices
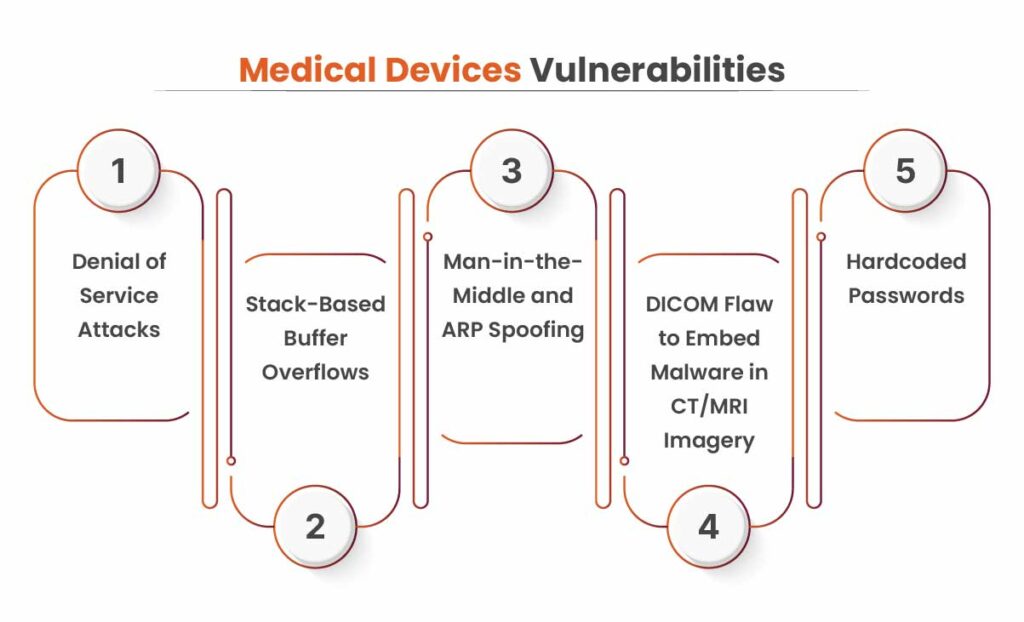
Below is the list of vulnerabilities in cyber attacks:
Denial of Service Attacks
Various medical devices use wireless networks to exchange information and data, which can create serious obstacles in achieving the security goals of integrity, confidentiality and availability.
Wireless networks are essentially radio signals transmitted between devices, which have been encoded to store and carry data. It is an EM wave that carries digital data and is vulnerable to interference from other EM waves. This presents two major security challenges:
- Jamming these signals is extremely simple and can prevent these devices from connecting to one another.
- It can be very difficult to track the source of the jamming or stop the jamming.
These types of attacks are known as denial of service attacks. These attacks affect the availability of information and can hamper the performance of medical devices. If a medical device is vulnerable to denial of service attacks, it can cause some serious security issues.
Stack Based Buffer Overflow
Stack-based buffer overflow attacks are used by the attackers to remotely take over the code execution of a process. Buffers refer to a system’s memory storage regions that hold the data temporarily while it is being transferred.
A buffer overflow takes place when the volume of data exceeds the memory buffer’s storage capacity. Consequently, the program trying to write the data overwrites adjacent memory locations.
To launch stack-based buffer overflow attacks, malicious actors leverage stack memory, which only exists during a function’s execution time. Through these attacks, malicious actors may gain elevated privileges inside your system. This vulnerability enables privilege escalation or remote code execution on the target system.
HL7 Protocol Vulnerable to Man-in-the-Middle and ARP Spoofing
This vulnerability is the unverified and unencrypted data standard widely used in the healthcare industry for almost all communications between systems. Typically, HL7 messages are transmitted to an interface engine, which transforms and distributes all the messages it receives to the appropriate outlying systems, helping all the data stay synced.
HL7 messages carry a healthcare organization’s most sensitive data. However, they are vulnerable to various cyber threats, especially Man-in-the-Middle (MITM) attacks.
The HL7 protocol does not address the two ways to combat MITM attacks- tampering detection and authentication. Without these controls, malicious actors can easily intercept communications between systems. There are numerous MITM techniques used by attackers; the most popular one is ARP (address resolution protocol) spoofing. Attackers can use ARP spoofing to launch MITM attacks and intercept traffic between endpoints.
To carry out these attacks, malicious actors send gratuitous ARP packets to the targeted system to re-associate their MAC address with another system’s legitimate IP addresses. Consequently, the traffic is redirected to the attackers instead of the legitimate secondary system. Often, the attacking system forwards the traffic in a way that neither system can detect interference.
Get in!
Join our weekly newsletter and stay updated
Exploitation of the DICOM Flaw to Embed Malware in CT/MRI Imagery
DICOM refers to a globally-recognized standard for the storage and exchange of medical images. It is used widely all across the healthcare industry ranging from the medical devices that produce imagery like MRI and CT machines. There is a flaw in the DICOM file format specification that enables malicious actors to embed executable code within the files.
By doing this, attackers can create a malicious hybrid file that is both a specification-compliant DICOM image, which can be viewed with any DICOM viewer as well as a fully-functioning windows executable. These files not only work like a typical Windows PE file but also adhere to the DICOM standard to preserve the patient information’s integrity.
Such files are referred to as PE/DICOM files. By exploiting this critical flaw, malicious actors can intertwine patient information with malware to easily and stealthily distribute it across a broad range of healthcare institutions.
Hardcoded Passwords
Medical devices containing hard-coded passwords are susceptible to an array of cyber threats. Hard-coded passwords refer to plain text (non-encrypted) credentials and other secrets like SSH keys implanted by the developers directly into the source code.
A wide range of medical devices, including ventilators, surgical and anesthesia devices, drug infusion pumps, patient monitors, laboratory and analysis equipment and external defibrillators use hard-coded credentials. The use of hard-coded passwords in medical devices is a huge risk as it makes it easy for malicious actors to discover confidential information by using password-guessing exploits.
This enables attackers to gain administrative access and high-level privileges by bypassing authentication. By exploiting hard-coded passwords, an attacker can gain access to biomedical information, calibration settings, network configuration, and device settings.
Book Your Free Cybersecurity Consultation Today!
How Kratikal Can Help in Medical Device Security Testing?
Kratikal specializes in medical device security testing, offering comprehensive solutions to identify and mitigate vulnerabilities in medical devices. Their approach includes penetration testing and vulnerability assessments to uncover potential design flaws in hardware, software, and communication protocols. By leveraging advanced methodologies like black-box, gray-box, and white-box testing, Kratikal ensures that medical devices meet stringent security standards. Their services help organizations enhance device security, protect sensitive patient data, and comply with industry regulations, ultimately safeguarding both healthcare providers and patients.
Conclusion
Vulnerabilities in medical devices pose a significant threat to the healthcare industry, potentially compromising patient safety, data security, and operational integrity. Cyber threats such as denial-of-service attacks, stack-based buffer overflow and much more highlight the urgency for stringent security measures. Addressing these vulnerabilities through regular security assessments, robust encryption, and compliance with industry standards is essential to protect sensitive medical information. As cyberattacks evolve, healthcare institutions must prioritize proactive cybersecurity strategies to mitigate risks and prevent catastrophic consequences.
FAQs
- What is medical device security?
Medical device security involves safeguarding medical devices and healthcare systems against cyber threats. The growing interconnectivity of medical devices, driven by IT/OT convergence, has heightened the need for robust security measures.
- What are device vulnerabilities?
A device vulnerability is a flaw or misconfiguration in its code base. Such vulnerabilities can be exploited to compromise the data within the device or the network it is connected to.



![5 Vulnerabilities in Medical Devices That Can Create Chaos [Updated]](https://kratikal.com/blog/wp-content/uploads/2021/12/medical-devices.jpg)





Leave a comment
Your email address will not be published. Required fields are marked *