Table of Contents
Understanding the Concept of Social Engineering
We are all aware of various types of attackers who are pro at using their technical expertise for data exploitation purposes. They aim at infiltrating protected computer systems and compromising user’s sensitive data. These attackers tend to stay a level ahead of the advanced technologies to bolster network defenses. However, to deploy malicious attacks, these attackers use a major weapon called social engineering.
Attackers are well aware of the fact that every organization has got one common weakness, which is human psychology. It is well known that humans are the weakest link in the chain of an organization’s cyber security.
With the help of phone calls and other communication mediums, these attackers trick people into giving away access to sensitive information of their organization.
Social engineering scams have been going on around the globe for many years. The term social engineering encompasses a wide spectrum of malicious activity.
There are five most common types of social engineering attacks. These attacks have been deployed worldwide by social engineers. Let’s proceed further for more details on these social engineering attacks.
Five Common Types of Social Engineering Attacks
1. Phishing
It is the most common but dangerous type of social engineering attack. Phishing attacks are infamously known for grabbing information from target uses. Phishers carry out this attack by sending malicious or spoofed emails to targets to get their personal information.
This attack is mainly deployed to accomplish three things:
-
- Obtain personal information like user’s credentials, social security numbers or financial details.
- Redirect users to suspicious websites, which host phishing landing pages.
- For the quick response from users by manipulating them with attempts of incorporating threats or show urgency.
Usually, phishing emails contain poor grammar, spelling errors or malicious attachments like doc files or URLs.
2. Quid Pro Quo
In this social engineering attack, hackers ask for critical data or login credentials in exchange for a service. For example, the hacker impersonates itself as a technical expert and phone calls an end-user. Then hacker offers a free service of IT assistance in exchange of user’s login credentials. Once the end-user is lured into handing over its secretive details, the hacker’s mission is accomplished. There are various ways to deploy this social engineering attack as fraudsters make victims believing it as a fair exchange.
3. Pretexting
Pretexting is equivalent to phishing activity. Here hackers create a false sense of trust to get information out of their victims. If a hacker targets an end-user then it impersonates itself as a user’s co-worker or a higher dignity from the user’s organization. By this, hacker wins user’s trust and easily gets access to user’s login credentials. These attacks shockingly come out to be effective and most of the sophisticated attackers use this method for the vicious intent.
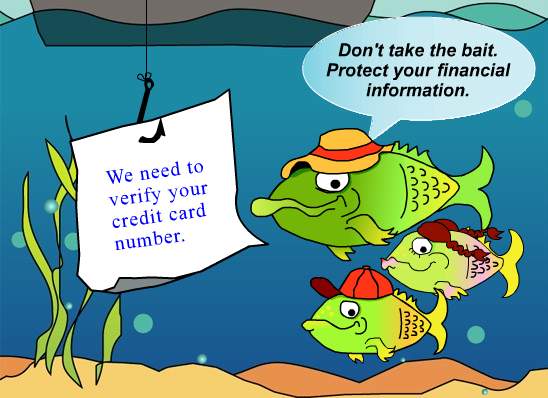
4. Baiting
Just like various similar phishing attacks, baiting is one of the ways to entice victims. In this social engineering attack, cyber-attackers promise goods or services to users in return for their login credentials. They use baits like “offer” or “free” downloads which could be of anything like movies, music, game, video, etc. Furthermore, it attracts users and they give away their login credentials easily. Baiting attacks do not restrict to online schemes. Attackers go way beyond to exploit human curiosity by using physical media too.
5. Piggybacking
Also known as tailgating, piggybacking is a practice of attackers trying to seek access to a restricted area. This attack is deployed when an unauthorized person physically follows the authorized person to a restricted place that lacks proper authentication. This type of social engineering attack can take place in any form. For instance, a hacker can either ask an employee to borrow his/her laptop for some work and can quickly install malware software stealthily.
How to Protect against Social Engineering Attack?
Social engineering attacks are occurring commonly nowadays and organizations are the prime targets. Since employees are the weakest link in the chain of an organization’s cyber security, it is important to educate them about cyber awareness. Tools like ThreatCop are highly recommended for spreading cyber awareness among employees, to ensure corporate cyber security.

ThreatCop by Kratikal is a risk assessment tool that checks and analyzes the vulnerability level of an organization. Further, it helps them in reducing the cyber risk up to 90%, within no time! This innovative tool by Kratikal has been recognized as the “Top-10” most innovative product of the year in 2017 by DSCI NASSCOM.
ThreatCop helps the organization in making their employees one of the strongest in the organization in terms of cyber security. Apart from that, this amazing tool empowers individuals by running a simulation attack of the latest cyber-attacks. This tool not only makes employees proactive but also helps in improving their level of vulnerability.
For Any Query:
- Email: [email protected]
- Contact: India (+91) 7428797201, USA (+1) 323 287 9435










Leave a comment
Your email address will not be published. Required fields are marked *